If you’re hosting your website and/or your email server on Google Cloud, you will need to create firewall rules to allow traffic to those virtual machine instances for specific ports requires for the services that operate on them.
Google cloud is great and affordable VDS (Virtual Dedicated Servers) hosting for those who know what they are doing. You can get a high powered virtual machine for a fraction of what it would cost you with a hosting provider, the catch is however on Google Cloud you manage everything yourself, and for most web or email hosting server setups you will need Linux and command line knowledge.
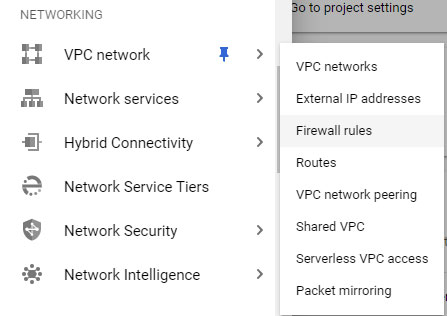
To create firewall rules, you use the Firewall Rules tool within the VPC Networks menu subset in the main menu of your Google Cloud Console interface.
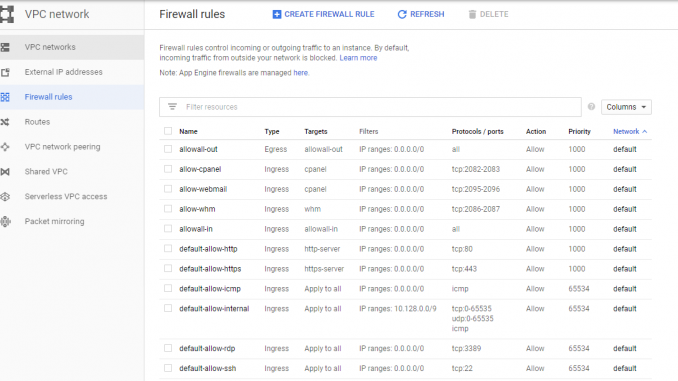
Once you have accessed the Firewall rules toolkit, you will be shown any firewall rules that have already been set up to use on your cloud network.
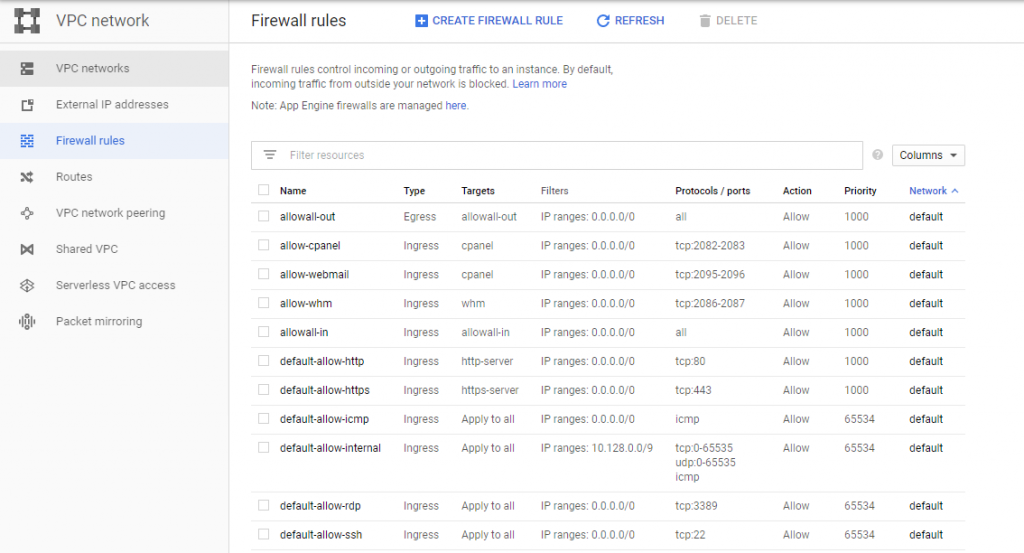
You can create additional firewall rules by clicking on the CREATE FIREWALL RULE option at the top of the page.

You will then need to enter details such as the name for the rule, which must contain no spaces.
You will also need to select whether the rule is for “Ingress” (Inbound) or “Egress” (Outbound) and whether the rule is to allow or deny traffic. You should usually make a rule for both inbound and another for outbound for most well used ports on website and email hosting servers.
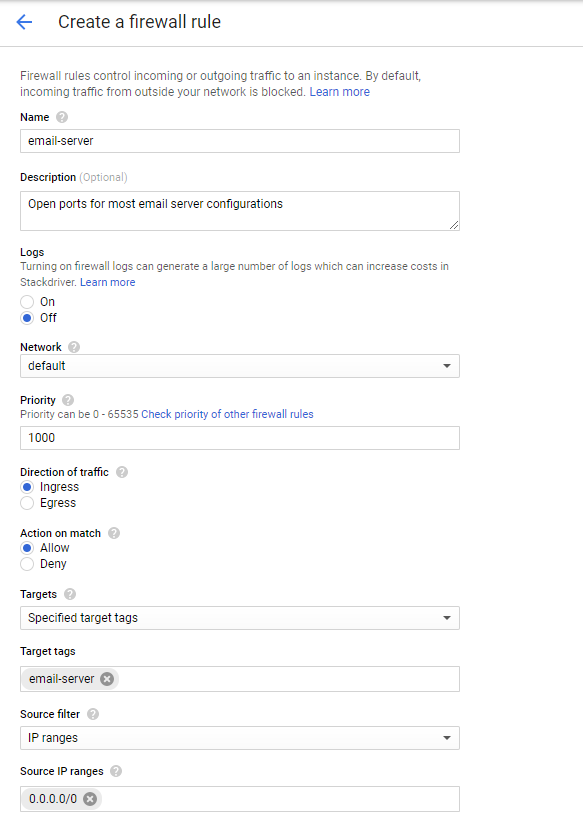
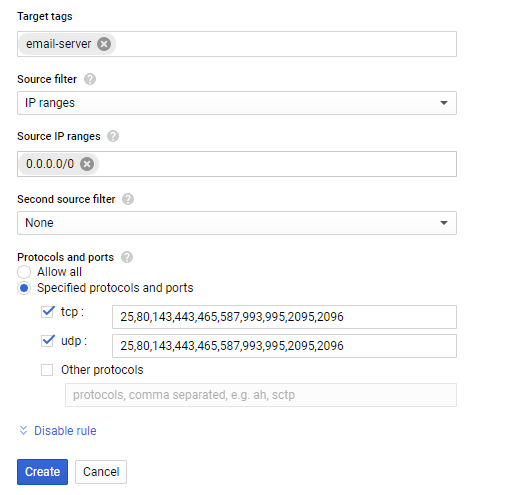
You will need to set the target for these, I recommend using Specified target tags and creating a tag that can be assigned to your VM’s (Virtual Machines) individually. Alternatively you can have it assign it to everything in your cloud network.
The Source filter in most cases with website and email hosting services, should be IP ranges, unless you want to lock down traffic to only a proxy, you should use the range 0.0.0.0/0 to allow traffic from anywhere.
You will also need to specify the ports that this firewall rule operates, common ports for different types of systems and functions are listed at the bottom of this post.
Once the rule is created, if you set the target to use tags, you will need to assign the tag to the VM in its setup, and this may require you to power down or reboot your VM
Common Ports for different server types to use in your firewall rules.
General website traffic
80 – General website traffic over non-SSL (insecure) connection.
443 – General website traffic over SSL (secure) connection.
cPanel Servers
2082 – cPanel access over non-SSL (insecure)
2083 – cPanel access over SSL (secure)
2086 – WHM access over non-SSL (insecure)
2087 – WHM access over SSL (secure)
2095 – Webmail over non-SSL (insecure)
2096 – Webmail over SSL (secure)
Email Servers
993 – IMAP over SSL (secure)
143 – IMAP over non-SSL (insecure)
995 – POP over SSL (secure)
110 – POP over non-SSL (insecure)
25 – Incoming SMTP authentication over non-SSL (insecure)
587 – SMTP/TLS Submission ofer non-SSL (insecure)
465 – SMTP/TLS Submission over SSL (secure)


Leave a Reply